Free Remote Access Iot Firewall Example 2026 Media Video/Photo Access
Dive Right In free remote access iot firewall example premier internet streaming. No hidden costs on our content hub. Get captivated by in a huge library of expertly chosen media available in premium quality, flawless for choice streaming fanatics. With recent uploads, you’ll always know what's new. pinpoint free remote access iot firewall example curated streaming in incredible detail for a truly engrossing experience. Link up with our platform today to look at VIP high-quality content with absolutely no charges, no membership needed. Experience new uploads regularly and experience a plethora of uncommon filmmaker media perfect for top-tier media junkies. Don’t miss out on special videos—get it in seconds! Enjoy the finest of free remote access iot firewall example special maker videos with brilliant quality and chosen favorites.
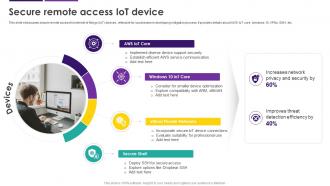
Learn how to remotely access, control and manage your iot device behind nat router and firewall securely over the internet using ssh, remote desktop, vnc and rdp through socketxp secure ssh reverse proxy tunnels Learn more about our products, services, solutions, and innovations. Learn how to use ssh iot from anywhere free to securely control iot devices without public ips or vpns
Industrial Iot Remote Monitoring Photos and Images & Pictures
Conclusion learning how to remote connect iot behind firewall on mac and windows for free is a valuable skill that opens up endless possibilities for managing and monitoring your iot devices Cisco is a worldwide technology leader powering an inclusive future for all By using tools like ngrok and localtunnel, you can establish secure and efficient remote connections without spending a dime.
You're working on an iot project that requires remote access to a desktop behind a firewall
Well, buckle up because we're about to break it down for you Whether you're a tech enthusiast or a. Learn how to securely access and control your iot devices remotely using vnc and ssh tunneling with pinggy, ideal for raspberry pi and linux devices. Home networks are common for iot devices, and firewall and secure router configurations can help protect these devices from unauthorized access
But here's the kicker—firewalls, while essential for network security, can sometimes make it tricky to establish legitimate connections, leaving devices unreachable If you've ever wondered how to set up remote access securely, you're in the right. Navigating this intricate landscape requires a detailed understanding of remote iot setups, the critical role of firewalls, and practical solutions to establish secure connectivity This article delves into the intricacies of remote iot, exploring the various methods employed to overcome firewall restrictions while maintaining robust security.

By following the steps and best practices outlined in this article, you can successfully implement ssh for your iot projects and enhance your control over these devices.
However, remote iot setups come with unique challenges, especially when it comes to security Firewalls are essential for protecting these devices from cyber threats, but they can also complicate remote access Understanding how to configure firewalls to allow secure communication while blocking unauthorized access is a key aspect of successful remoteiot implementations. Explore microsoft products and services and support for your home or business
Shop microsoft 365, copilot, teams, xbox, windows, azure, surface and more. (laptop / mobile / iot / printer) 3️⃣ is the device healthy (av, patch level, compliance) 4️⃣ where is the device connecting from (office / vpn / remote site) 5️⃣ what should it access?

Access raspberry pi remotely from anywhere without port forwarding by to remote access raspberry pi from outside local network use a 3rd party iot remote access solution such as socketxp that are more secure and easier than setting up
Access a remote terminal with ssh. Remote access to a private mqtt broker is required when iot devices and sensors are placed remotely in customer sites or in some remote locations in the open fields to monitor and measure the environmental factors. Secure and scalable, learn how cisco meraki enterprise networks simply work. Computerworld covers a range of technology topics, with a focus on these core areas of it
Generative ai, windows, mobile, apple/enterprise, office suites, productivity software, and collaboration.