Remoteiot Behind Firewall Examples Full Library HQ Vids/Pics Direct
Launch Now remoteiot behind firewall examples deluxe content delivery. No strings attached on our visual library. Plunge into in a enormous collection of videos unveiled in high definition, suited for high-quality streaming junkies. With recent uploads, you’ll always know what's new. Find remoteiot behind firewall examples chosen streaming in impressive definition for a truly enthralling experience. Hop on board our media world today to look at subscriber-only media with zero payment required, no membership needed. Get frequent new content and investigate a universe of distinctive producer content crafted for prime media fans. Be sure not to miss specialist clips—download quickly! Enjoy the finest of remoteiot behind firewall examples special maker videos with rich colors and hand-picked favorites.
Remoteiot behind firewall examples highlight the importance of secure and efficient network configurations in modern iot deployments By understanding the security challenges, implementing best practices, and leveraging the latest tools and technologies, organizations and individuals can achieve secure and reliable remote access to iot devices. The process of remote iot behind firewall represents a significant advancement in how organizations manage and secure their connected devices
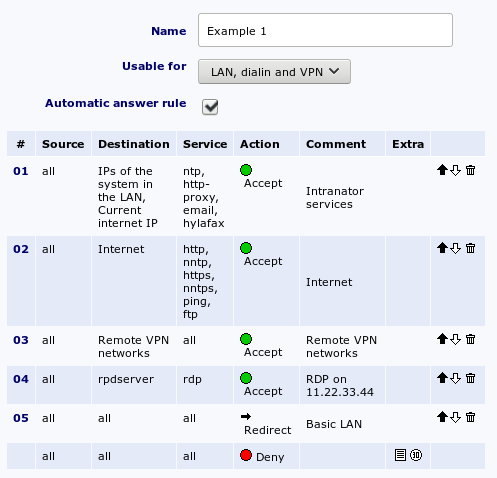
Firewall ruleset examples & policy best practices | AlgoSec
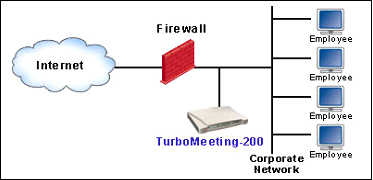
By understanding the nuances of this approach, businesses and tech enthusiasts alike can leverage the power of iot while maintaining robust protection against cyber threats. Remote iot connections behind firewalls are a critical component of modern iot systems Properly configuring a firewall is vital to enable remote access while maintaining security
This includes identifying required ports and protocols, as well as employing secure authentication methods
Several tools and technologies are available to facilitate remote iot management. Remoteiot behind firewall examples provide valuable insights into how organizations can maintain robust cybersecurity while enabling seamless connectivity There are several ways to securely access iot devices remotely over the internet, but the most common ones involve leveraging specific technologies and configurations. In today's connected world, enabling remote iot operations within secure networks is a hot topic among tech enthusiasts and professionals alike
Whether you're managing smart home devices or industrial sensors, understanding remote iot behind firewall examples is crucial for ensuring seamless connectivity while maintaining robust security. Learn how to remotely access, control and manage your iot device behind nat router and firewall securely over the internet using ssh, remote desktop, vnc and rdp through socketxp secure ssh reverse proxy tunnels Remoteiot behind firewall examples showcase how organizations can overcome these challenges The ability to securely access iot devices from anywhere is vital for industries such as manufacturing, healthcare, and transportation

Remoteiot solutions enable technicians and operators to monitor and control devices without compromising security.
Common approaches to remote iot access behind firewalls overcoming the firewall barrier requires creative strategies that either tunnel through the firewall, leverage intermediary services, or initiate connections from the inside out. Remote iot deployments often face challenges when it comes to securely accessing devices behind firewalls As businesses embrace the internet of things (iot) for enhanced efficiency and connectivity, ensuring secure communication between remote systems and centralized networks becomes paramount This article dives deep into remote iot behind firewall examples, offering practical solutions and.
How does a remoteiot firewall work It can block or allow traffic based on factors like ip addresses, ports, and protocols Some advanced firewalls even use machine learning algorithms to detect and respond to potential threats automatically. Remoteiot behind firewall examples highlight the importance of configuring firewalls to allow legitimate traffic while denying malicious attempts

In conclusion, remoteiot behind firewall examples demonstrate the importance of secure and efficient remote access for iot devices
By understanding the challenges, solutions, and best practices outlined in this guide, businesses can implement effective strategies for protecting their iot ecosystems. In today's interconnected world, iot remote control behind firewall example has become a crucial topic for both businesses and individuals looking to secure the This article delves into various remote iot behind firewall examples, exploring the technologies and strategies that enable devices to operate effectively without compromising network integrity. Remoteiot behind firewall examples demonstrate how organizations can maintain robust security while ensuring seamless access to their iot infrastructure
In this guide, we'll break down everything you need to know about remote connect iot behind firewall examples From setting up secure connections to troubleshooting common issues, we'll walk you through every step. A remoteiot firewall serves as a critical security layer designed to protect iot devices from unauthorized access and cyber threats These firewalls are specifically tailored to address the unique challenges posed by the growing number of connected devices in remote environments.

The manufacturing plant's network is protected by a firewall, ensuring that only authorized traffic can pass through
Remoteiot solutions provide a mechanism for these iot devices to securely send data to the server, even behind the firewall This allows the plant engineers to monitor and control the operation of the plant from anywhere in the. Remote iot behind firewall refers to the ability of iot devices to communicate and share data with external systems while being protected by a firewall Think of a firewall as a digital bouncer at a club, deciding who gets in and who doesn't.